Here is a quick summary for you; see bottom of post for a detailed guide.
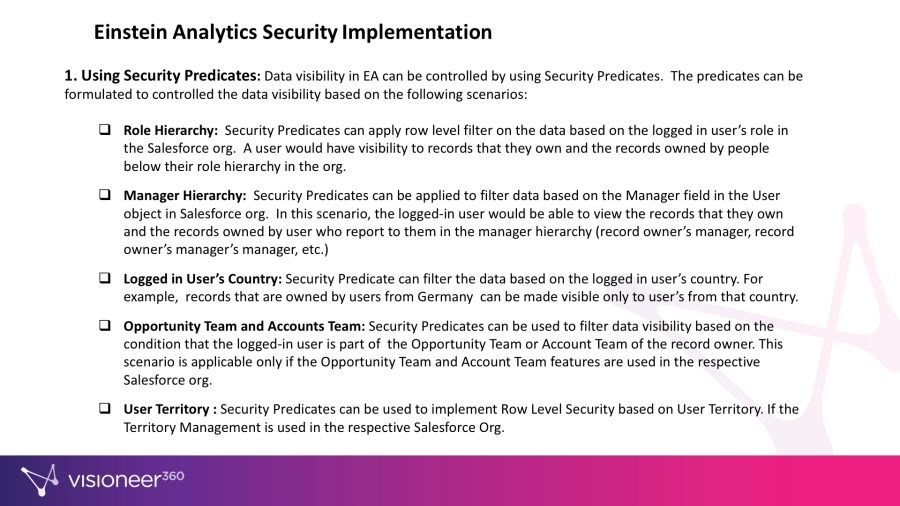
1. Using Security Predicates
Data visibility in EA can be controlled by using Security Predicates. The predicates can be formulated to control the data visibility based on the following scenarios:
- Role Hierarchy: Security Predicates can apply row level filter on the data based on the logged in user’s role in the Salesforce org. A user would have visibility to records that they own and the records owned by people below their role hierarchy in the org.
- Manager Hierarchy: Security Predicates can be applied to filter data based on the Manager field in the User object in Salesforce org. In this scenario, the logged-in user would be able to view the records that they own and the records owned by user who report to them in the manager hierarchy (record owner’s manager, record owner’s manager’s manager, etc.)
- Logged in User’s Country: Security Predicate can filter the data based on the logged in user’s country. For example, records that are owned by users from Germany can be made visible only to user’s from that country.
- Opportunity Team and Accounts Team: Security Predicates can be used to filter data visibility based on the condition that the logged-in user is part of the Opportunity Team or Account Team of the record owner. This scenario is applicable only if the Opportunity Team and Account Team features are used in the respective Salesforce org.
- User Territory : Security Predicates can be used to implement Row Level Security based on User Territory. If the Territory Management is used in the respective Salesforce Org.
2. EA Application and Dashboard level Access Implementation
The EA Dashboards should be stored in individual EA Apps in order to control user access. For example, Executive Dashboard and Sales Representative Dashboards cannot be saved in the same Application. The should be split across two EA Applications. Access to the two EA applications can be controlled by maintaining two different public groups in the Salesforce org.
3. EA Access Permissions
Access to EA functionalities like create / modify dashboards, lenses and dataflows can be controlled by configuring the EA Permission sets.
4. Salesforce Sharing Inheritance
While this functionality can be used, we do not recommend it for a variety of reasons, including the amount of space the sharing rules consume in the EA instance, and other limitations. Refer to Salesforce BI Data Integration Guide (link found below).